Malwarebytes Premium Crack Latest Version With Keygen Full Download

It’s hard to beat Malwarebytes Crack when it comes to anti-virus protection. Viruses, malware, and spyware of the highest level can all be removed. Auto-scan is enabled and your computer’s performance is improved. Malwarebytes can be used on laptops, and Macs, and detects all types of viruses. It is compatible with all operating systems. This is a highly intelligent piece of anti-malware software that keeps an eye out for other, less obvious malware tools. An Antivirus program can be found using Malwarebytes Crack. Malwarebytes is an excellent anti-virus program.
Does free download Malwarebytes Premium crack 2022 is that the riskiest application for automatically scanning malware? This program starts out as an infection scanner and then adds a lot of extra features that you can turn off. This is usually a very smart security programmer that looks for more trustworthy malware that you can’t find. Malware-bytes Crack figures out which antivirus code is the most effective. Malwarebytes is a great virus protection program. Once it gets going, it checks your laptop for viruses very quickly.
Malwarebytes Premium With Full Working Keys:
Additionally, Malwarebytes Full Version Crack allows you to cool down your CPU as it heats up due to the heavy workload. This provides the best services for CPU management, but it also activates the scanning process. While scanning, it is able to remove all of the errors and correct all of the mistakes at the same time. Despite the name implying otherwise, the real goal of this piece of software is to keep your devices safe from all manner of malicious software such as viruses and worms, rootkits, rogue programs, and spyware. Your devices will be shielded from scams and bogus websites thanks to this useful software project.
In the event that you have malware on your computer, Malwarebytes Crack can automatically detect it and remove it without any hassle. This program’s sole purpose is to protect you from ransomware. To top it all off, Malwarebytes full Torrent lets you remove any and all installed threats. Moreover, emerging threats can disrupt the system before it is disrupted. It’s a handy application with an appealing user interface. You don’t have to be concerned about customers when you use this program to play online, buy, and connect.
Malwarebytes Serial Key Features:
- Systems that are susceptible to attack are protected.
- Modified scripts can now be run.
to be deleted, a delete reboot is executed - There are four ways to conduct system scans
- Zero-time detection and elimination
- An instrument for raising the alarm
- Stop the spread of ransomware
- Anti-malware technology
- Many Malwarebytes are integrated.
- adware, malware, and the like.
- All network endpoints are detected.
- scan the system in accordance with the needs of the user.
- Find, control, manage and monitor endpoints using asset management
- Enables a more effective option.
- It’s a complete threat.
- Getting to the right place was a snap.
- interface for entering commands through a terminal
- sanitize the infected machines
- In the fight against malicious software
- Coordinated administration
- The term “permanent” refers to software that has been installed for an extended period
- Report the most serious dangers to your organization.
- automate the removal of malware infection.
- A list of well-known worms, Trojans, and ads
- Push installation options are available in a variety of configurations.
- A preventative measure.
You may also download Divvy crack
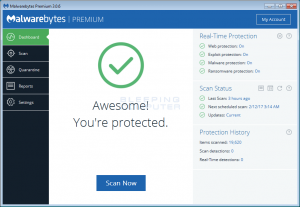
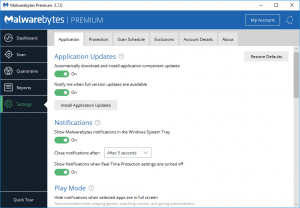
ScreenShots:

What’s New In Malwarebytes With Registration Key?
- Notifies us if the papers and envelopes contain dangerous elements.
- Removing browser-based malware is essential.
- Anti-Malware settings that will help you shine.
- It has support for multiple languages.
Malwarebytes Premium Crack Benefits:
- Recognizes untrustworthy systems
- As a result of the endpoint, it is easier to identify and manage security threats
- End-user productivity is preserved and maintained.
- The efficiency of the computer system
- Damage inflicted on the victim of abuse.
- On a per-hour basis, IT resources
- Zero-hour malware prevention
- Protects the endpoints and the entire scale.
- Your endpoints and installed software are discovered by this tool
- Defends against the deportation of data
- Deploying and managing technology becomes more efficient.
- Protection safeguards unsupported software
- This is a weak point. Provides security for the endpoints
- Cyber assault victims can easily be safeguarded.
- Streamlined administration
- Your business is gaining ground and becoming more successful.
- Protects the genetic code
- Viruses that are able to evade typical security measures.
- Exceptional accomplishments
- Enhances output.
- Defending against quantifiable threats
- The absence of malware on a network system.
System Requirements:
- OS: Windows 7, 8, 10, 11, XP, Vista [32-bit & 64-bit]
- CPU: At least Pentium IV with a 1.2 GHz processor
- Memory: At least 1 GB
- Disk Space: 120 MB for the setup
- Active internet connection
Malwarebytes Crack (100%) Working Keys:
Serial Key [2022]:
- CE4SX-AZWSX-E4TFV-6BGY7-BGFVD
- CXZAW-3E4SX-DCRTF-V6GYB-F4S3W
License Key [New]:
- 6787G-DIOKE3-VSNKJ3-CDSJJK-VDSAA
- GSG5G-FAEEW-VFVADA-TYRIIE-VFDA3
- HVBHJ-53DFFS-TRYCF-YTDSS-AESSA-43444
- CRTFV-3SXE4-DC5RF-V6TVG-VFVADA
- ESZ3W-53DFFS-TRYCF-YTDSS-AESSA-5645
How to Crack Malwarebytes?
- First and foremost delete the old version.
- Click the given link below to install the latest version.
- It takes some time to install properly.
- At the end of installing process, a shortcut will appear.
- Run the File and enjoy the newest version.
- Thank you, Have fun with it.






Leave a Reply